Active Projects
|
Securing the web's public key infrastructure |
|
The importance of the web's public key infrastructure (PKI) cannot be overstated: it provides users with the ability to verify with whom they are communicating online, and enables encryption of those communications. While the online use of the PKI is mostly automated, there is a surprising amount of human intervention in management tasks that are crucial to its proper operation. This project investigates the roles played by all of the PKI's principals: website administrators, browsers, certificate authorities, and content delivery networks (CDNs). Only by understanding the humans in the loop can we hope to truly secure this critical infrastructure. Key findings:
|

|
Provably avoiding nation-state censorship |
|
Traditional Internet communication leaves communicating parties vulnerable to persecution and disruption from online censorship. Although there are many systems in active use today that seek to resist censorship through anonymous, confidential communication (most notably Tor), they are currently rather brittle in the presence of a large censoring regime. In particular, some countries censor not just their own citizens' traffic, but any traffic that happens to pass through their borders. In this project, we are developing new systems that empower users with greater control over where their packets don't go. Rather than rely on inaccurate maps of the Internet, we use novel measurement techniques and universal constraints like the fact that information cannot travel faster than the speed of light to provide provable guarantees. Key contributions:
|
|
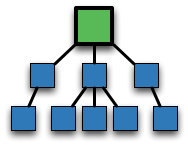
Measuring DNS from the root |
|
The Domain Name Service (DNS) is responsible for converting human-readable domain names (like www.cs.umd.edu) to an Internet-routable IP address (128.8.127.30). Without it, the Internet would be largely unusable. DNS is made up of a hierarchical namespace, and its 13 roots (A-root through M-root) are run by separate entities. These root servers are some of the most critical pieces of network infrastructure. The University of Maryland has always run D-root. Working with UMD's Division of IT, we have been collecting and analyzing data about how root servers are used, misused, and abused. Key contributions:
|

|
Finer-grained cloud computing |
|
Today's cloud computing platforms have pricing models that work very well for popular servers or computationally-intensive tasks like protein folding. However, they are ill-suited to tasks that are long-lived but mostly idle, such as personalized servers. In this project, we are developing a new approach to cloud computing that only consumes (and charges for) precisely the resources needed to run a process. This results in lower costs to users, more efficient pricing models for cloud providers, and avenues to more secure cloud computing. Key contributions:
|

|
Secure programming competitions |
|
Despite the increased attention to security as a first-order design principle, many developers continue to produce insecure software, which remains vulnerable despite billions spent annually on security appliances and other defenses. We believe this situation arises, at least in part, from a lack of evidence and education. For example, code reviews, penetration testing, and static code analysis are all known to improve security by finding vulnerabilities, but the relative costs and benefits of these techniques are largely unknown. As a remedy to this state of affairs, we have developed and continue to run a secure coding contest called Build-it Break-it Fix-it that seeks to (1) give student contestants a competitive setting to learn about secure software creation and (2) experimentally measure the outcomes of the contest to add to the evidence of what works and what does not. Key contributions:
|
Past Projects
|
Peer-to-peer incentives |
|
The Internet is no longer the collaborative playground it once was; it now comprises millions of corporate entities and billions of users who often have their own conflicting interests. In addition to acts of malice, there are rampant acts of selfishness wherein users seek to gain from the network, regardless of what impact this might have on others. Unfortunately, the Internet's protocols are not suited to support self-interest. This project seeks to analyze existing protocols' susceptibility to selfish manipulation, and to develop new systems that perform correctly and efficiently, even if all participants act selfishly. At the core of this work is the practical application of game theory and mechanism design to large-scale, decentralized systems. Key contributions:
|