Mazurek and Akgul Win Distinguished Paper Award at USENIX
A University of Maryland-led team recently received a distinguished paper award for delving into the challenges faced by bug bounty hunters—ethical hackers who discover and report vulnerabilities or bugs to a platform’s developer.
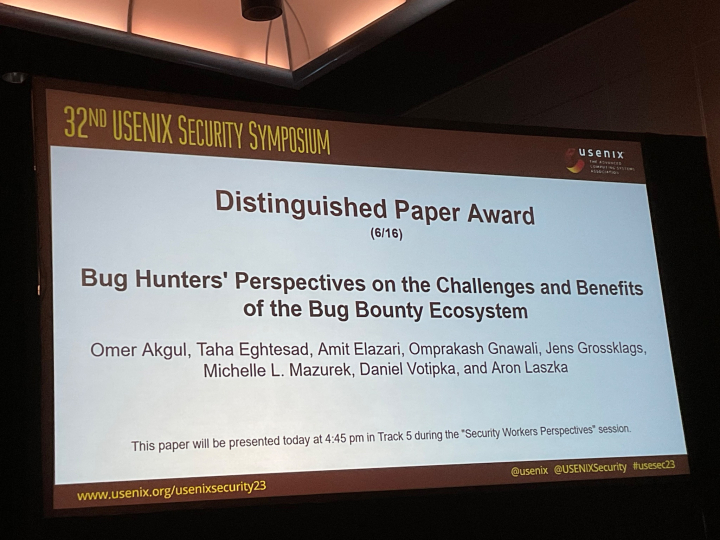
Researchers from the Department of Computer Science, including a graduate student and a faculty member who also serves as the director of the Maryland Cybersecurity Center (MC2), earned honors at the 32nd USENIX Security Symposium. The symposium, held August 9–11 in Anaheim, California, gathered professionals from various fields to discuss recent breakthroughs in computer systems and network security and privacy.
The paper, “Bug Hunter’s Perspectives on the Challenges and Benefits of the Bug Bounty Ecosystem,” seeks to understand the difficulties that individuals in bug-bounty programs must navigate. First spearheaded by Netscape in 1995, many companies—including Google and Apple—and governmental agencies now run bug-bounty programs. When the ecosystem functions well, bug bounties have the potential to improve the security posture of organizations—commercial or governmental—at a low cost.
The researchers found communication problems, such as unresponsiveness and disputes, are most likely to discourage bug hunters. They offer recommendations to make the bug-bounty ecosystem more accommodating and ultimately increase participation in an underutilized market.
The award-winning team is comprised of Omer Akgul, lead author and a seventh-year Ph.D. student; Michelle Mazurek, an associate professor of computer science and director of MC2; Daniel Votipka, an assistant professor of computer science at Tufts University who received his Ph.D. from UMD in 2020; and researchers from Pennsylvania State University, University of Houston, Technical University of Munich, and University of California, Berkeley.
Four additional papers by MC2 researchers were presented at USENIX and the 19th Symposium on Usable Privacy and Security (SOUPS), a co-located conference.
Three of the papers contain qualitative studies of interviews with privacy and security challenges faced by various groups—including library IT staff, professional product reviewers, and teenagers using virtual reality (VR). The fourth paper explores strategies to circumvent censorship in China.
The other MC2-affiliated papers are:
“How Library IT Staff Navigate Privacy and Security Challenges and Responsibilities” presents 12 interviews with library IT staff members regarding their privacy and security protocols and policies, the challenges they face implementing them, and how this all relates to their patrons. They discovered that the participants are primarily concerned with protecting their patrons’ privacy from threats outside their walls, such as police and government authorities and third parties, and occasionally from other patrons who also use the devices. MC2-affiliated authors are Alan F. Luo (lead author), Noel Warford (lead author), Samuel Dooley and Michelle Mazurek.
“The Role of Professional Product Reviewers in Evaluating Security and Privacy” shares insights from 17 interviews with product reviewers about their procedures, incentives and assumptions regarding security and privacy on Internet-connected devices and software. They found that while reviewers have incentives to consider security and privacy, they face significant disincentives and challenges, including audience disinterest, lack of expertise, potentially unreliable assumptions, and a dearth of effective and usable tools for evaluation. MC2-affiliated authors are Wentao Guo (lead author), Jason Walter and Michelle Mazurek.
“How the Great Firewall of China Detects and Blocks Fully Encrypted Traffic” measures and characterizes the Great Firewall of China’s (GFW) new system for censoring fully encrypted traffic. The researchers’ understanding of the GFW’s new censorship mechanism helps them derive several practical circumvention strategies. They responsibly disclosed their findings and suggestions to the developers of different anti-censorship tools, helping millions of users successfully evade this new form of blocking. MC2-affiliated authors are Danesh Sivakumar, Kevin Bock and Dave Levin.
“An Investigation of Teenager Experiences in Social Virtual Reality from Teenagers’, Parents’, and Bystanders’ Perspectives” presents an interview study with 24 participants—eight teenagers, seven parents and nine bystanders—to understand how they perceive threats and the mitigation strategies they employ. The team uncovered several safety threats that teenagers may face, such as virtual grooming, ability-based discrimination, unforeseeable threats in privacy rooms, and more. Their findings provide a better understanding of the risks teens face in social VR, and offer insights to design safer and more fulfilling experiences. The MC2-affiliated author is Julio Poveda (paper appeared at SOUPS).
—Story by Melissa Brachfeld, UMIACS communications group
The Department welcomes comments, suggestions and corrections. Send email to editor [-at-] cs [dot] umd [dot] edu.